One of my occasional consulting customers called me in a panic because all of their HP printers printed out the same page at the same time:
GET http://ipv4scan.com/hello/check.txt HTTP/1.1
Host: ipv4scan.com
Accept-Encoding: gzip, deflate, compress
Accept: */*
User-Agent: IPv4Scan (+http://ipv4scan.com)
Now, I have nothing against most network measurement bots. Most are useful, and the rest are usually well-intentioned, even if they are counterproductive. The one thing these have in common is that they have a page that tells you what they’re doing, why they’re doing it, and who to contact if you have further questions.
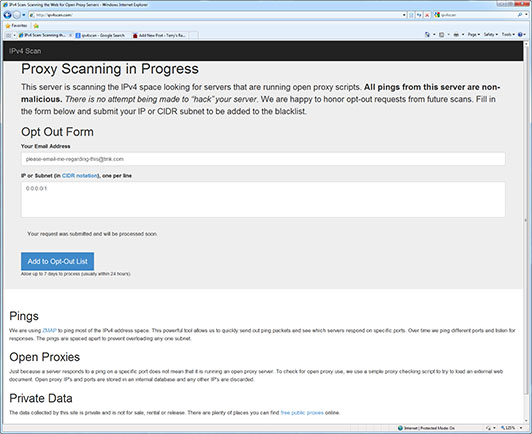
The http://IPv4Scan.com page does none of those:
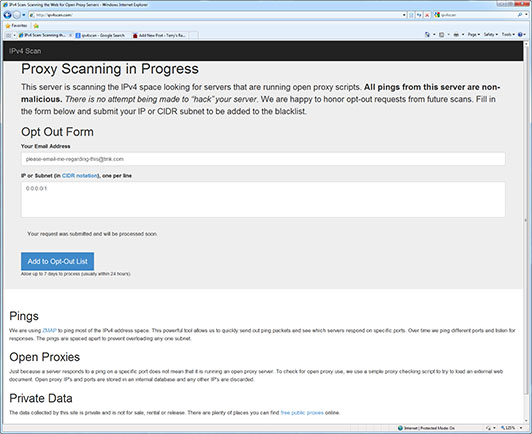
There is no contact information provided on the page, there is no statement of how the data is being used (other than that it is “not for sale, rental or release”). The web page source does not contain any useful contact information, either. So they’re collecting this data for their own, unspecified, purposes.
Ok, maybe it is legit, just with a spectacularly bad public relations campaign. Let’s look and see who is behind this:
(0:115) host:~terry# jwhois ipv4scan.com
[whois.internet.bs]
Domain Name: IPV4SCAN.COM
Registry Domain ID: 1824307886_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.internet.bs
Registrar URL: http://www.internetbs.net
Updated Date: 2013-08-30T10:37:11Z
Creation Date: 2013-08-30T10:21:44Z
Registrar Registration Expiration Date: 2014-08-30T10:21:44Z
Registrar: Internet.bs Corp.
Registrar IANA ID: 814
Registrar Abuse Contact Email: abuse@internet.bs
Registrar Abuse Contact Phone:
Reseller:
Domain Status: clientTransferProhibited
Registry Registrant ID:
Registrant Name: Domain Administrator
Registrant Organization: Fundacion Private Whois
Registrant Street: Attn: ipv4scan.com, Aptds. 0850-00056
Registrant City: Panama
Registrant State/Province:
Registrant Postal Code: Zona 15
Registrant Country: PA
Registrant Phone: +507.65967959
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: 5230a6158jiing35@5225b4d0pi3627q9.privatewhois.net
Registry Admin ID:
Admin Name: Domain Administrator
Admin Organization: Fundacion Private Whois
Admin Street: Attn: ipv4scan.com, Aptds. 0850-00056
Admin City: Panama
Admin State/Province:
Admin Postal Code: Zona 15
Admin Country: PA
Admin Phone: +507.65967959
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: 5230a6157t3qutyb@5225b4d0pi3627q9.privatewhois.net
Registry Tech ID:
Tech Name: Domain Administrator
Tech Organization: Fundacion Private Whois
Tech Street: Attn: ipv4scan.com, Aptds. 0850-00056
Tech City: Panama
Tech State/Province:
Tech Postal Code: Zona 15
Tech Country: PA
Tech Phone: +507.65967959
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: 5230a615n285uy95@5225b4d0pi3627q9.privatewhois.net
Name Server: ns-canada.topdns.com
Name Server: ns-usa.topdns.com
Name Server: ns-uk.topdns.com
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2014-04-29T05:00:41Z <<<
Ok, so they're hiding behind a privacy service, but seem to be located in Panama. Let's see if the IP address they're using matches:
(0:116) host:~terry# host ipv4scan.com
ipv4scan.com has address 93.174.93.51
ipv4scan.com mail is handled by 5 smtp09.topdns.com.
ipv4scan.com mail is handled by 5 smtp01.topdns.com.
(0:117) host:~terry# jwhois 93.174.93.51
[whois.ripe.net]
% This is the RIPE Database query service.
% The objects are in RPSL format.
%
% The RIPE Database is subject to Terms and Conditions.
% See http://www.ripe.net/db/support/db-terms-conditions.pdf
% Note: this output has been filtered.
% To receive output for a database update, use the "-B" flag.
% Information related to '93.174.93.0 - 93.174.93.255'
% Abuse contact for '93.174.93.0 - 93.174.93.255' is 'admin@ecatel.net'
inetnum: 93.174.93.0 - 93.174.93.255
netname: NL-ECATEL
descr: ECATEL LTD
descr: Dedicated servers
descr: http://www.ecatel.net/
country: NL
admin-c: EL25-RIPE
tech-c: EL25-RIPE
status: ASSIGNED PA
mnt-by: ECATEL-MNT
mnt-lower: ECATEL-MNT
mnt-routes: ECATEL-MNT
source: RIPE # Filtered
role: Ecatel LTD
address: P.O.Box 19533
address: 2521 CA The Hague
address: Netherlands
abuse-mailbox: abuse@ecatel.info
remarks: ----------------------------------------------------
remarks: ECATEL LTD
remarks: Dedicated and Co-location hosting services
remarks: ----------------------------------------------------
remarks: for abuse complaints : abuse@ecatel.info
remarks: for any other questions : info@ecatel.info
remarks: ----------------------------------------------------
admin-c: EL25-RIPE
tech-c: EL25-RIPE
nic-hdl: EL25-RIPE
mnt-by: ECATEL-MNT
source: RIPE # Filtered
% Information related to '93.174.88.0/21AS29073'
route: 93.174.88.0/21
descr: AS29073, Route object
origin: AS29073
mnt-by: ECATEL-MNT
source: RIPE # Filtered
% This query was served by the RIPE Database Query Service version 1.72 (DBC-WHOIS3)
So, they're using an IP address allocated to Ecatel in the Netherlands. Not exactly close to Panama, is it? Let's see if that address is actually in the Netherlands:
(0:118) host:~terry# traceroute ipv4scan.com
traceroute to ipv4scan.com (93.174.93.51), 64 hops max, 52 byte packets
[snip]
8 be2094.ccr21.bos01.atlas.cogentco.com (154.54.30.14) 20.530 ms
be2097.ccr22.bos01.atlas.cogentco.com (154.54.30.118) 19.664 ms
be2095.ccr21.bos01.atlas.cogentco.com (154.54.30.38) 20.657 ms
9 be2387.ccr22.lpl01.atlas.cogentco.com (154.54.44.166) 85.582 ms 85.667 ms
be2386.ccr21.lpl01.atlas.cogentco.com (154.54.44.162) 85.388 ms
10 be2183.ccr42.ams03.atlas.cogentco.com (154.54.58.70) 95.882 ms
be2182.ccr41.ams03.atlas.cogentco.com (154.54.77.245) 95.035 ms
be2183.ccr42.ams03.atlas.cogentco.com (154.54.58.70) 97.517 ms
11 be2311.ccr21.ams04.atlas.cogentco.com (154.54.74.90) 130.510 ms
be2312.ccr21.ams04.atlas.cogentco.com (154.54.74.94) 94.574 ms
be2311.ccr21.ams04.atlas.cogentco.com (154.54.74.90) 101.849 ms
12 149.11.38.179 (149.11.38.179) 101.548 ms 118.302 ms 102.141 ms
13 server.anonymous-hosting-service.com (93.174.93.51) 98.234 ms 97.335 ms 96.958 ms
Ok, the server is in Amsterdam, Netherlands. But hiding behind anonymous-hosting-service.com seems suspicious. Let's see where they are:
(0:119) host:~terry# jwhois anonymous-hosting-service.com
[Querying whois.verisign-grs.com]
[Redirected to whois.onlinenic.com]
[Querying whois.onlinenic.com]
[whois.onlinenic.com]
Domain Name: anonymous-hosting-service.com
Registry Domain ID:
Registrar WHOIS Server: whois.onlinenic.com
Registrar URL: http://www.onlinenic.com
Updated Date: 2014-04-06 03:14:38
Creation Date: 2009-09-08
Registrar Registration Expiration Date: 2015-09-08
Registrar: Onlinenic Inc
Registrar IANA ID: 82
Registrar Abuse Contact Email: onlinenic-enduser@onlinenic.com
Registrar Abuse Contact Phone: +1.5107698492
Domain Status: clientTransferProhibited
Registry Registrant ID:
Registrant Name: Laura Yun
Registrant Organization: Vindo International Ltd.
Registrant Street: Oliaji TradeCenter - 1st floor
Registrant City: Victoria
Registrant State/Province: Mahe
Registrant Postal Code: 5567
Registrant Country: SC
Registrant Phone: +248.6629012
Registrant Phone Ext:
Registrant Fax: +248.24822575500
Registrant Fax Ext:
Registrant Email: anonymous.client@vindohosting.com
Registry Admin ID:
Admin Name: Laura Yun
Admin Organization: Vindo International Ltd.
Admin Street: Oliaji TradeCenter - 1st floor
Admin City: Victoria
Admin State/Province: Mahe
Admin Postal Code: 5567
Admin Country: SC
Admin Phone: +248.6629012
Admin Phone Ext:
Admin Fax: +248.24822575500
Admin Fax Ext:
Admin Email: anonymous.client@vindohosting.com
Registry Tech ID:
Tech Name: Laura Yun
Tech Organization: Vindo International Ltd.
Tech Street: Oliaji TradeCenter - 1st floor
Tech City: Victoria
Tech State/Province: Mahe
Tech Postal Code: 5567
Tech Country: SC
Tech Phone: +248.6629012
Tech Phone Ext:
Tech Fax: +248.24822575500
Tech Fax Ext:
Tech Email: anonymous.client@vindohosting.com
Name Server: ns1.anonymous-hosting-service.com
Name Server: ns2.anonymous-hosting-service.com
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2014-04-06 03:14:38 <<<
Well, this is definitely fishy. No legitimate survey would be hiding behind so many levels of indirection.
I used the site's form to "opt out" 0.0.0.0/1 with an email address requesting they contact me about their project. I've also sent email to the abuse contacts shown above, pointing them to this blog entry, in the hope that they can get some sort of explanation from their customer.
In the meantime, you may want to fine-tune your firewall rules to prevent this type of probe. That would (at a minimum) include blocking all outside connection attempts on ports 80 (http) and 443 (https) to anything on your network that is not intended to be a public web server. I cannot recommend using their opt-out form as there is no indication of what they do with the information. For all I know, it has the same effect as sending "unsubscribe" in response to a spam email - it just targets you for more spam.
If I receive any information from my inquiries, I'll update this blog entry accordingly.